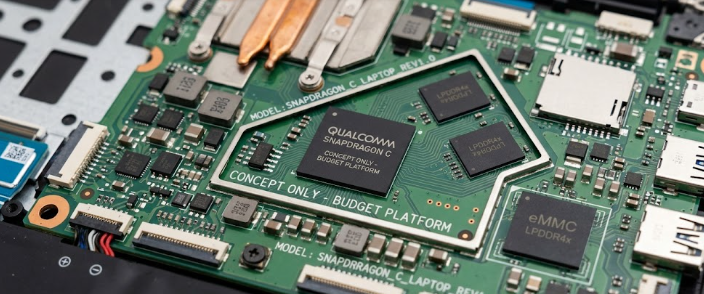
The tech world is witnessing a massive shift in how companies build budget computers. Tech leaders just dropped some exciting news during the global pre-Computex 2026 briefings. Qualcomm unveiled a brand-new processor line that aims to change cheap laptops forever. Instead of making cut-down versions of their expensive computer chips, they are doing something different. They are moving their highly efficient smartphone technology straight into laptops. This strategy centers on the new Snapdragon C chips, which aim to power ultra-budget Windows and Googlebook laptops costing between $300 and $500.
The Smart Engineering Shift Behind Snapdragon C Chips
To understand this shift, we must look at how engineers design computer processors. Usually, chipmakers try to shrink big computer chips to fit into cheaper laptops. This time, Qualcomm flipped the script by upgrading its phone-first Kryo processor layouts for laptops. Since a laptop body is much larger than a smartphone, engineers have more room to manage heat.
Consequently, this extra space allows the Snapdragon C chips to run at peak performance without overheating. Furthermore, Qualcomm can mass-produce these processors at rock-bottom prices because they already make similar phone chips by the millions. This clever engineering choice gives budget laptops a massive boost without raising production costs.
+————————————————————-+
| QUALCOMM’S STRATEGY SHIFT |
+————————————————————-+
| OLD WAY: Shrink complex, expensive PC chips -> Too Costly |
| |
| NEW WAY: Upgrade efficient phone chips -> Ultra-Budget |
+————————————————————-+
Breaking the 20-Hour Battery Barrier
The biggest benefit of using mobile phone technology in a laptop is energy efficiency. Smartphone chips inherently operate on a much lower wattage floor than traditional laptop processors. Therefore, laptops using these new processors require very little power to run daily tasks.
Because of this efficiency, the first commercial laptops using this platform promise incredible battery life. For instance, the newly unveiled Acer Aspire Go 15 (AG15-Q31P) promises a true 20-hour baseline runtime. In addition, these laptops achieve this milestone using fanless, hyper-portable designs. You can finally leave your charger at home without worrying about your battery dying.
Bringing Local AI to Cheap Laptops
Budget laptops usually miss out on modern artificial intelligence features due to weak hardware. However, Qualcomm is changing this narrative by adding a dedicated Neural Processing Unit (NPU) to this budget platform. Even though these laptops are cheap, they can still handle smart tasks locally.
Clearly, these Snapdragon C chips lack the high TOPS (Trillions of Operations Per Second) rating required for Microsoft’s elite Copilot+ PC club. Even so, the built-in NPU brings impressive local AI capabilities to the ultra-budget tier. For example, your laptop can handle real-time voice filtering and camera background blur during video calls. As a result, you get a smoother video setup without slowing down your computer.
Hidden Technical Tradeoffs in Budget Designs
While these advancements sound amazing, manufacturers must make tough choices to keep laptop prices under $400. Buyers need to watch out for certain memory and architecture bottlenecks before purchasing. Brands must decide whether to deploy standard DDR4 memory or the faster LPDDR5 RAM.
| Feature | Budget Option | Premium Option | Impact on User |
| System Memory | DDR4 RAM | LPDDR5 RAM | Affects overall multitasking speed |
| Storage Type | UFS Memory | True SSD | Affects file transfer and boot times |
Similarly, storage performance depends heavily on the internal components. Brands are balancing whether to use true SSD controllers or phone-grade UFS memory to hit that low sweet spot. While UFS memory saves money, it cannot match the speed of a true solid-state drive. Therefore, you should check these hidden specs closely when shopping for these laptops.
To learn more about the technical details of modern computer hardware and mobile silicon architecture, visit AnandTech for in-depth technology reviews.
References
- Qualcomm Pre-Computex 2026 Briefings.
- Acer Aspire Go 15 (AG15-Q31P) Product Announcement.




