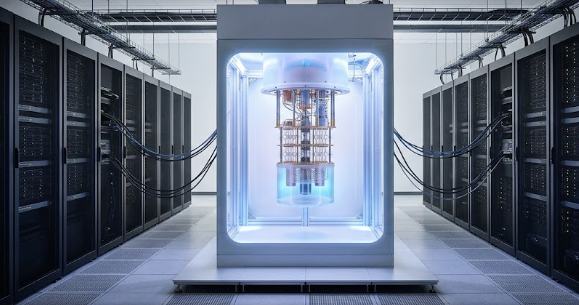
Smart homes just got a major brain boost. Google recently rolled out its May 2026 Spring Upgrade for Google Home. This exciting update brings native Gemini intelligence directly to your Nest smart cameras. In the past, smart cameras could only detect basic motion or simple objects. Today, the new Google Gemini for Home Upgrade introduces something called Multimodal Context-Aware Vision.
This advanced technology allows your home security cameras to understand complex human behaviors. Consequently, your cameras can now trigger intricate smart home routines based entirely on visual context. If you want to know how this changes everything, let us dive into the details.
Natural Language Triggers Replace Complex Coding
The Google Gemini for Home Upgrade completely changes how we set up smart home automation. Previously, homeowners had to program static, rigid motion logic into their apps. You had to draw digital boxes on your screen and hope for the best. Now, you can use simple English to tell your house what to do.
Because of this update, you can simply type or speak natural instructions into your app. For example, you can tell your system: “If you see the dog standing by the backdoor for more than 30 seconds, trigger the smart pet door to unlock.” The AI understands the context of the dog’s behavior. Therefore, it executes the command perfectly without any complicated setup.
Contextual Parsing vs Basic Motion Sensed
To truly appreciate the Google Gemini for Home Upgrade, we must look at how it handles data. Traditional cameras often spam your phone with useless notifications. A blowing leaf or a passing car can easily trigger an annoying alert. However, this new cloud-hybrid processing loop fixes that problem completely.
The system easily distinguishes between different visual actions. For instance, the camera knows when a courier drops off a package on your porch. It will immediately trigger a useful alert for you. Conversely, if a neighbor simply walks past your porch, the AI suppresses the notification. This smart filtering ensures that your phone only buzzes when something truly matters.
Expanding the Smart Ecology Chain
The power of the Google Gemini for Home Upgrade goes far AI alerts. Instead, these visual triggers branch beautifully across your entire smart home ecosystem. Your cameras now act as the main eyes for all your connected devices. As a result, your home reacts to your movements in real-time.
Imagine walking up to your house with heavy bags of groceries. The outdoor camera detects you carrying groceries toward the kitchen. Immediately, it pops open the smart lock for you. Simultaneously, it triggers the smart refrigerator to illuminate its interior and dims the ambient living room lighting down to your favorite preset profile. This seamless interaction makes life incredibly convenient.
The 19-Country Token Protocol for Enhanced Security
Security and privacy are major concerns for every homeowner today. Thankfully, Google designed this upgrade with strict privacy rules in mind. This feature is currently in an Early Access phase across 19 countries. It uses a very secure system called the 19-Country Token Protocol to protect your personal data.
This protocol implements strict end-to-end encryption on all visual metadata packets. In simple terms, the AI analyzes your behavior patterns safely. It never creates unencrypted, vulnerable server-side video logs that hackers could steal. Therefore, you get all the benefits of advanced automation without sacrificing your family’s privacy.
To learn more about setting up your connected devices safely, check out this guide on Smart Home Automation Tech.
References
- Google Home Official Blog (May 2026 Spring Upgrade Release Notes)
- Nest Labs Security and Encryption Whitepaper 2026
- Journal of Multimodal AI and Domestic Automation Systems